Cloud Services

Cloud Computing has clocked bullish adoption in the past few years, with the global market standing at a staggering figure of $214.3 billion in 2019, pointing to a 17.5% yearly growth. With organizations increasingly exploring cloud-first strategies, the entire IT industry is witnessing an upheaval.
Cloud architectures come in multiple forms, each with its own position in the tech stack:
- • Infrastructure as a Service (IaaS):Virtualization of core network infrastructures such as data center servers and storage.
• Platform as a Service (PaaS): Streamlining of redundant IT tasks such as app development and operating system management.
• Software as a Service (SaaS): A hosted version of the software with costs incurred on a usage basis.
Every category has its own security requirements and responsibilities that are divided between the cloud service provider and the customer. The choice of cloud deployment model also has a similar bearing.
Importance of Cloud Customer Architectures
Cloud customer architectures are descriptions of the required elements to implement specific application solutions that are using cloud services. They are important since they:
- • Empower cloud customers to grasp the USPs and the importance of using cloud computing.
- • Bridge the gap between cloud customer needs and offerings of cloud providers.
- • Guide customers on how business apps can be realized and deployed from the perspective of cloud customers.
- • Enable customers to be more productive, saving valuable time and resources.
Best Practices for Securing Cloud Workloads
While every cloud environment has an element of uniqueness, they share certain common characteristics where risks can be mitigated. Let’s look at some proven practices to help secure workloads on the cloud.
1. Researching ideal recommendations of the cloud service provider
Based on your choice of the cloud service provider, there is always an ideal set of recommendations for security infrastructure design and application configuration. This includes management steps related to identifying, categorizing, and protecting assets on the cloud, creating users and groups, securing data, operating systems, and applications on the cloud, and much more. A firm understanding of each of these is directly correlated to a secure cloud environment.
2. Understanding the shared responsibility model
When it comes to cloud, security remains a shared responsibility. While the cloud provider is responsible for the uptime, updates, and upgrades of the cloud platform, users on the public cloud are responsible for protecting applications and data. Understanding this model includes awareness of the fact that most data breaches occur when customers do not appreciate data security protocols.
3. Identifying weak points to minimize damage
However robust your cloud environment seems to be, there are always certain weaknesses that need to be mitigated. Internal errors, such as a misconfiguration, can easily manifest into security loopholes in the absence of fallback plans. Efficient management here involves defining roles and responsibilities, response mechanisms, and service level agreement (SLA) standards. The next step is to create a security incident response rulebook that establishes proper governance, risk, and compliance models.
4. Implementing a Zero Trust protocol
Having a ‘No Trust’ policy quickly translates to the practice of verifying all internal and external requests. This means that all security and monitoring services are correctly set up, and violations are immediately reported. This should include validation of containers or code that are downloaded from public repositories.
5. Introducing security measures to control and monitor network traffic
This includes controlling and monitoring both inbound and outbound traffic to distinguish between legitimate and illegitimate requests. The idea is to protect the integrity of internal servers in sensitive situations such as data thefts or unwarranted communication with command and control systems.
6. Implementing Identity and Access Management
Identity and Access Management involves authentication and authorization of cloud users, extending user-specific cloud permissions, and more. This also involves setting up and maintaining three primary elements for the cloud environment, such as – cloud user role, device type, and access type. Key components of this step include Identity lifecycle management, Segregation of duties, Privileged Account Management (PAM), and Multifactor authentication (MFA), among others.
7. Managing application-level security
Constant vulnerability management, deployment of the ideal security measures, and an in-depth understanding of threats play an important role at the application level. Protection of digital assets begins at the development level where developers manage security requirements by ensuring that applications adhere to both national and international security standards. This includes steps such as:
• Analysing the surface of attacks
• Service and data-level isolation
• Web application scanning
• Penetration testing
8. Applying security monitoring & vulnerability management
Security monitoring involves proactively monitoring, tracking, identifying, and reacting to security incidents. This ends up creating the entire audit history of compliance and incident management that varies according to the cloud deployment model and cloud service category.
Vulnerability management is another facet that requires focus on heads such as:
- • Monitoring lists of Common Vulnerability Exposure (CVE)
• Actively identifying and prioritizing relevant vulnerabilities
• Developing a remediation plan for vulnerabilities
• Tests to verify the remediation of vulnerabilities
Looking at the Future
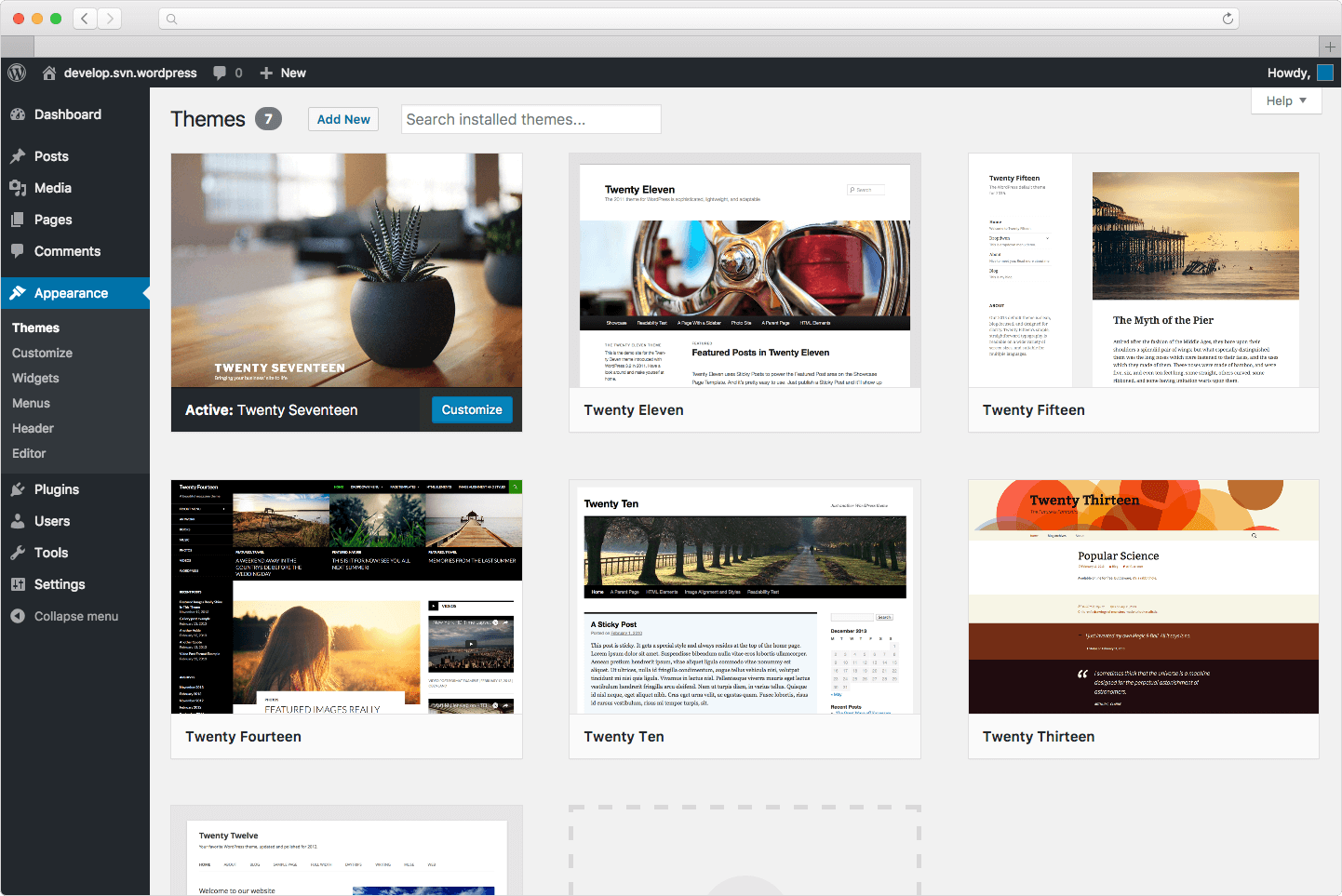
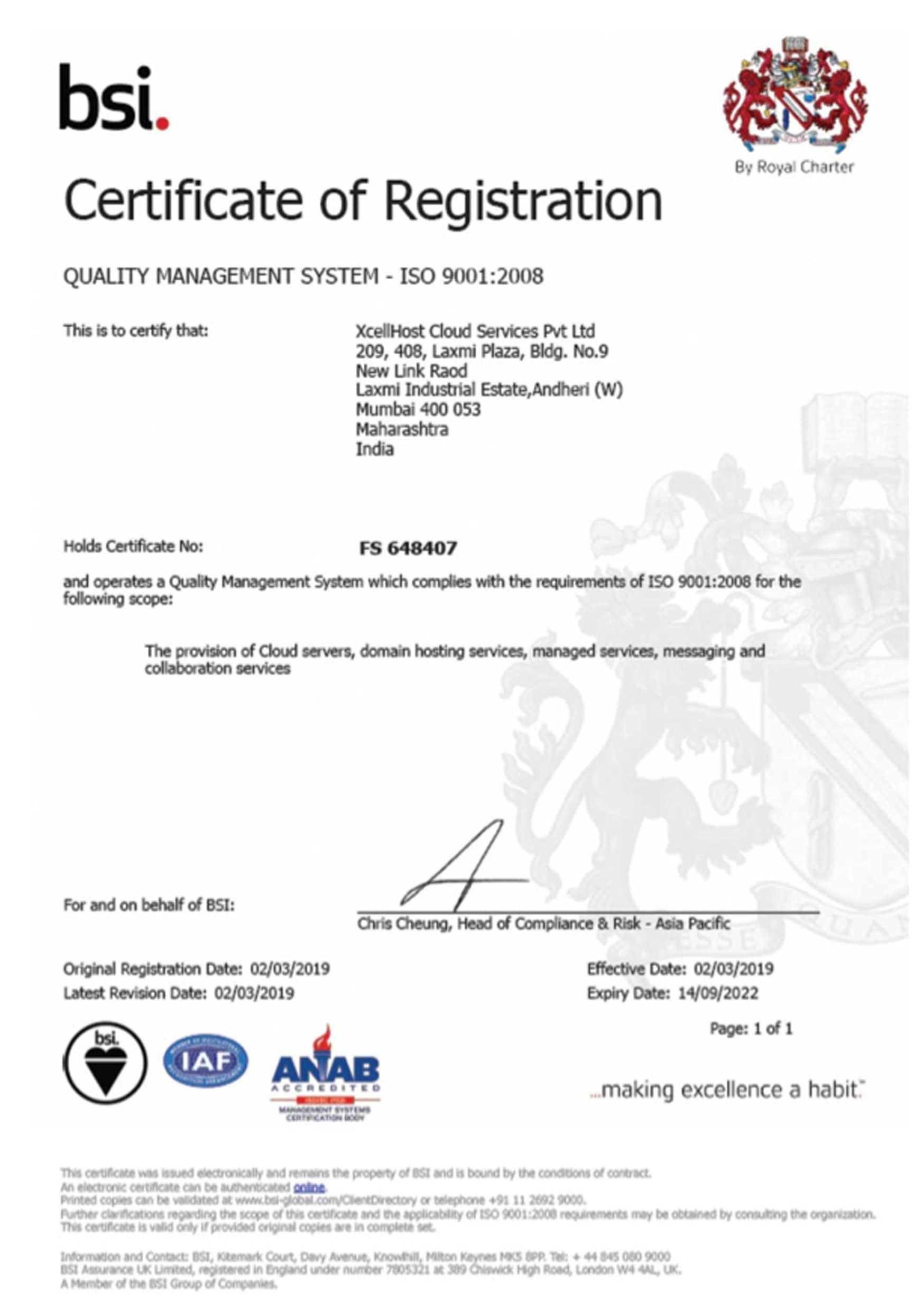
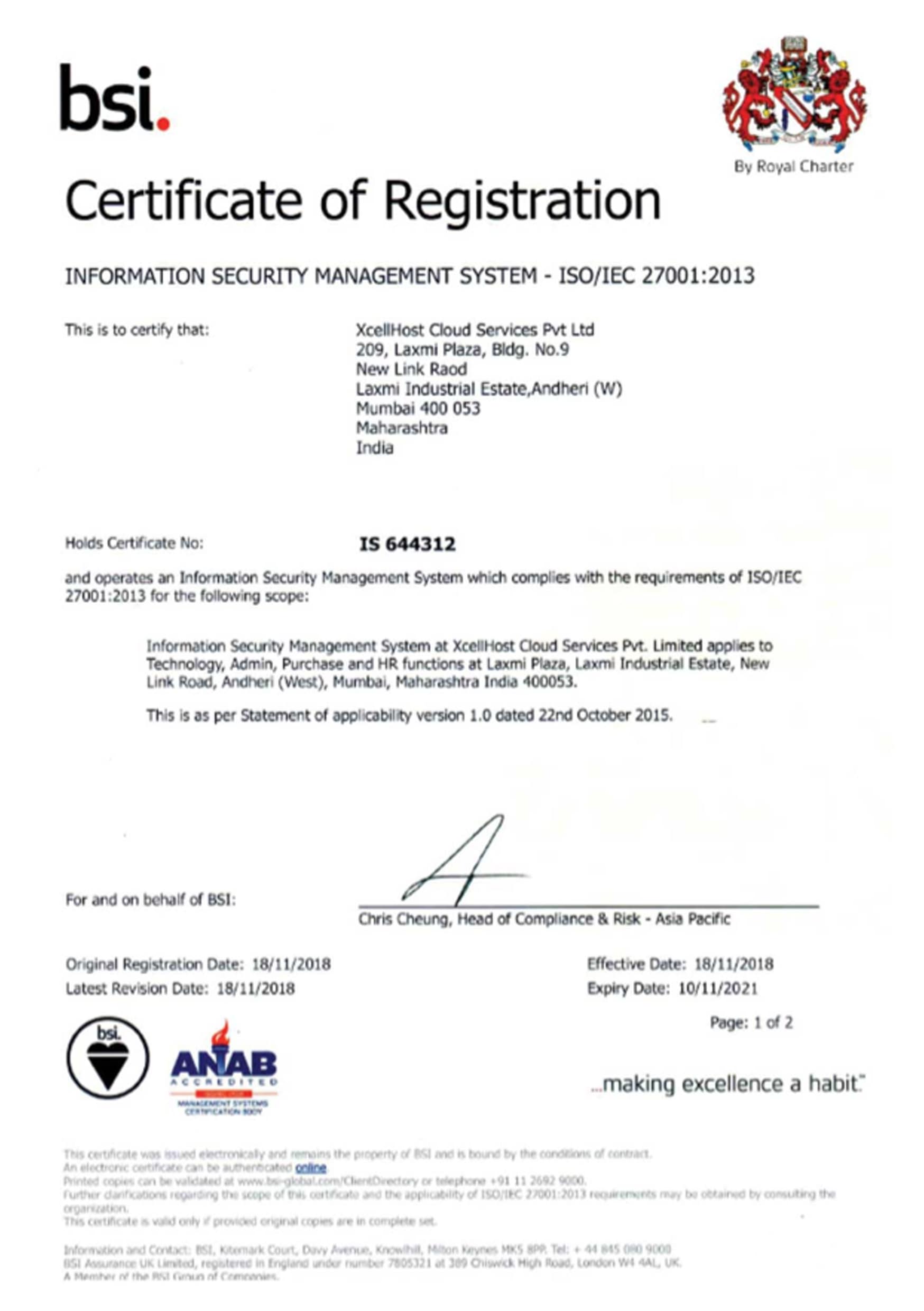
The ability to rapidly scale their cloud environments on a per-needs basis is working well for companies with high growth potential. And since cloud does include certain security risks, secure management of workloads in the cloud is only slated to increase in importance. The XcellHost's Cloud platform has been intricately developed by following every aforementioned security protocol. With a clear understanding of cloud service models and aligning with cybersecurity and compliance standards, XcellHost ensures that you maintain a strong security posture since day one.
Schedule a demo today to learn more about our platform and how you can leverage it to run secure workloads through compliant cloud environments.
 +91-22-40074555 | Ext.1
+91-22-40074555 | Ext.1